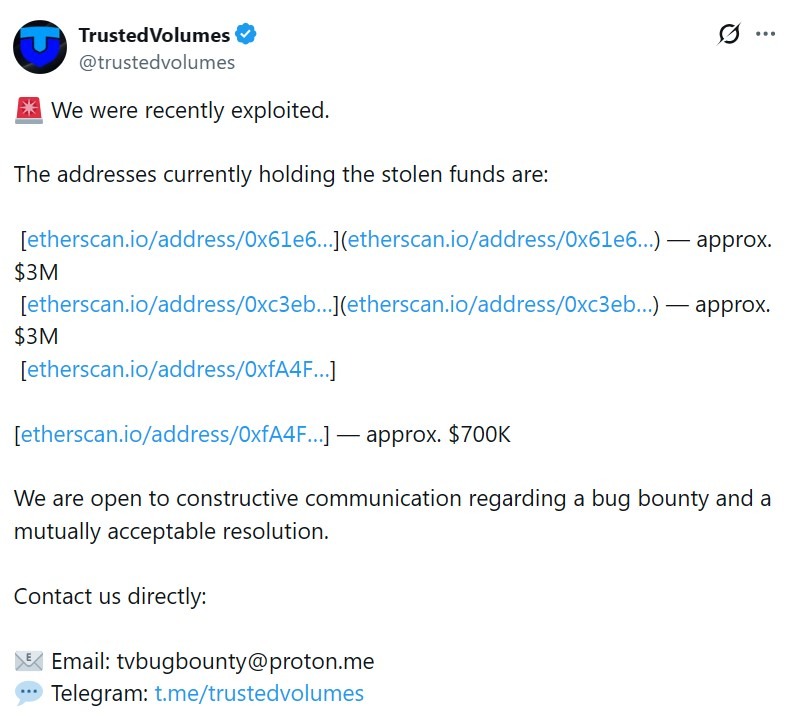
TrustedVolumes, an independent market maker and analyst used by 1inch Fusion, confirmed the exploit and said about $6.7 million in stolen funds were held across three Ethereum addresses.
In a Thursday post TrustedVolumes said it was open to “constructive communications” about bug bounty and a “mutually acceptable solution.”
The confirmation came after Web3 security firm Blockaid said its exploit detection system had identified an ongoing Ethereum exploit targeting TrustedVolumes. Blockaid said the attack involved custom swap infrastructure controlled by TrustedVolumes. Blockaid initially estimated that about $5.87 million had been mined, including Wrapped Ether, USDT, Wrapped Bitcoin, and USDC.
Blockchain security firm CertiK said the attacker registered as an authorized order signer through a public function, and then used that authorization to execute orders that transferred funds from targets.
The incident highlights the risks surrounding third-party infrastructure used to implement a decentralized exchange, where analysts and market makers can run their own contracts even when the underlying protocol and ordinary users are not directly affected. TrustedVolumes independently acts as a liquidity provider for multiple protocols, including 1inch, which said its systems, infrastructure and user funds were not affected.
Cointelegraph reached out to TrustedVolumes for additional comment but did not receive a response upon publication.
source: Reliable storage units
1 Inch says none of its protocols were violated
In an The platform said there was “no impact on 1inch’s systems, infrastructure or user funds.”
Sergey Kunz, co-founder of 1 Inch, said TrustedVolumes operates independently and is not limited to 1 Inch. “Although 1inch uses TrustedVolumes as an analyst, we are one of many companies,” Kunz said.
Framing the exploit as a 1-inch-related incident was “confusing and harmful,” Kunz said, adding that 1-inch is monitoring the situation with security partners and will assist where appropriate.
Related to: Andre Cronje says DeFi is ‘no longer DeFi’ as builders debate circuit breakers
Security researcher Vladimir Sobolev, known as Officer Notes on
Sobolev said the exploit points to broader weaknesses in cryptocurrency security practices, as vulnerabilities can quickly lead to immediate losses.
“We lack security in general,” Sobolev told Cointelegraph. “Blockchain tends to have an immediate reward.” “We need to pay more attention to stop switches, monitoring, circuit breakers, etc.”
Both Blockaid and Sobolev noted that the attack was carried out by the same operator responsible for the 1inch Fusion V1 analyzer exploit in March 2025. However, Blockaid said the latest attack involved a different vulnerability.
In March 2025, 1inch said that a vulnerability affected solvers using the legacy Fusion v1 implementation in their own contracts, while end-user funds remained safe. SlowMist later traced about $5 million in stolen assets, including USDC and Wrapped Ether.
1inch and the affected analyst negotiated with the attacker, who returned most of the stolen funds under a bug bounty agreement, according to 1inch and Decurity’s postmortem.
magazine: North Korea Denies Cryptocurrency Hacks, Upbit Bank Tests Ripple: Asia Express
On-chain analysis shows that the stolen assets were quickly split across multiple wallets. A portion of the funds was swapped into stablecoins, while some were bridged across different blockchains to make tracking more difficult. Security researchers believe the attacker may have used mixing services to further obscure the flow of funds.
The Resolver development team has acknowledged the breach and confirmed that a critical patch is under development. They have also advised users to withdraw remaining assets from the protocol as a precautionary measure. Trading activity linked to Resolver tokens dropped sharply following the announcement, reflecting panic among investors.
Security firms assisting in the investigation are currently tracing the movement of funds using blockchain forensics tools. However, recovery remains uncertain, as a portion of the assets may already be beyond traceable routes.
The incident has reignited concerns about the security of DeFi protocols, particularly those relying on complex smart contract interactions and cross-chain routing systems. Experts note that even minor vulnerabilities in such systems can lead to large-scale exploits.
Community discussions across forums and social media platforms have intensified, with users demanding accountability, audits, and potential compensation. Some governance proposals are already being discussed, including emergency upgrades and possible reimbursement mechanisms.
Meanwhile, market sentiment around Resolver-linked assets remains negative, with liquidity providers withdrawing and token prices under pressure. The broader DeFi sector is also watching closely, as this exploit adds to a growing list of security incidents in decentralized finance.
Investigations are still ongoing, and a full post-mortem report is expected once analysis is complete.